Security compliance is no longer optional for organizations handling customer data. SOC 2 and ISO 27001 are the two most widely adopted security frameworks, yet they serve different regulatory, operational, and market needs.
This guide explains how each framework works and how to choose the right one.
SOC 2 is an assurance framework that evaluates how organizations protect customer data across defined trust principles.
It is widely required by the U.S.-based enterprises, regulated industries, and B2B SaaS vendors. SOC 2 focuses on operational effectiveness, not formal certification.
According to the American Institute of CPAs (AICPA), SOC 2 reports validate how security controls function over time, not how they are documented.
SOC 2 evaluates controls using 5 Trust Services Criteria (TSC). Organizations select criteria based on their risk profile and customer obligations.
ISO 27001 is an international standard for establishing and maintaining an Information Security Management System (ISMS).
It is recognized across Europe, Asia, the Middle East, and regulated global markets. ISO 27001 focuses on systematic risk management, governance, and continuous improvement.
According to ISO.org, certified organizations demonstrate formal alignment with global security best practices.
ISO 27001 requires documented risk management and governance controls. Certification is issued by an accredited external body after a formal audit.
SOC 2 validates operational controls, while ISO 27001 certifies governance and risk management maturity.
Both frameworks address security but answer different stakeholder questions.
SOC 2 answers “Are your controls working today?”
ISO 27001 answers “Is your security program systematically managed?”
SOC 2 vs ISO 27001 Comparison Table
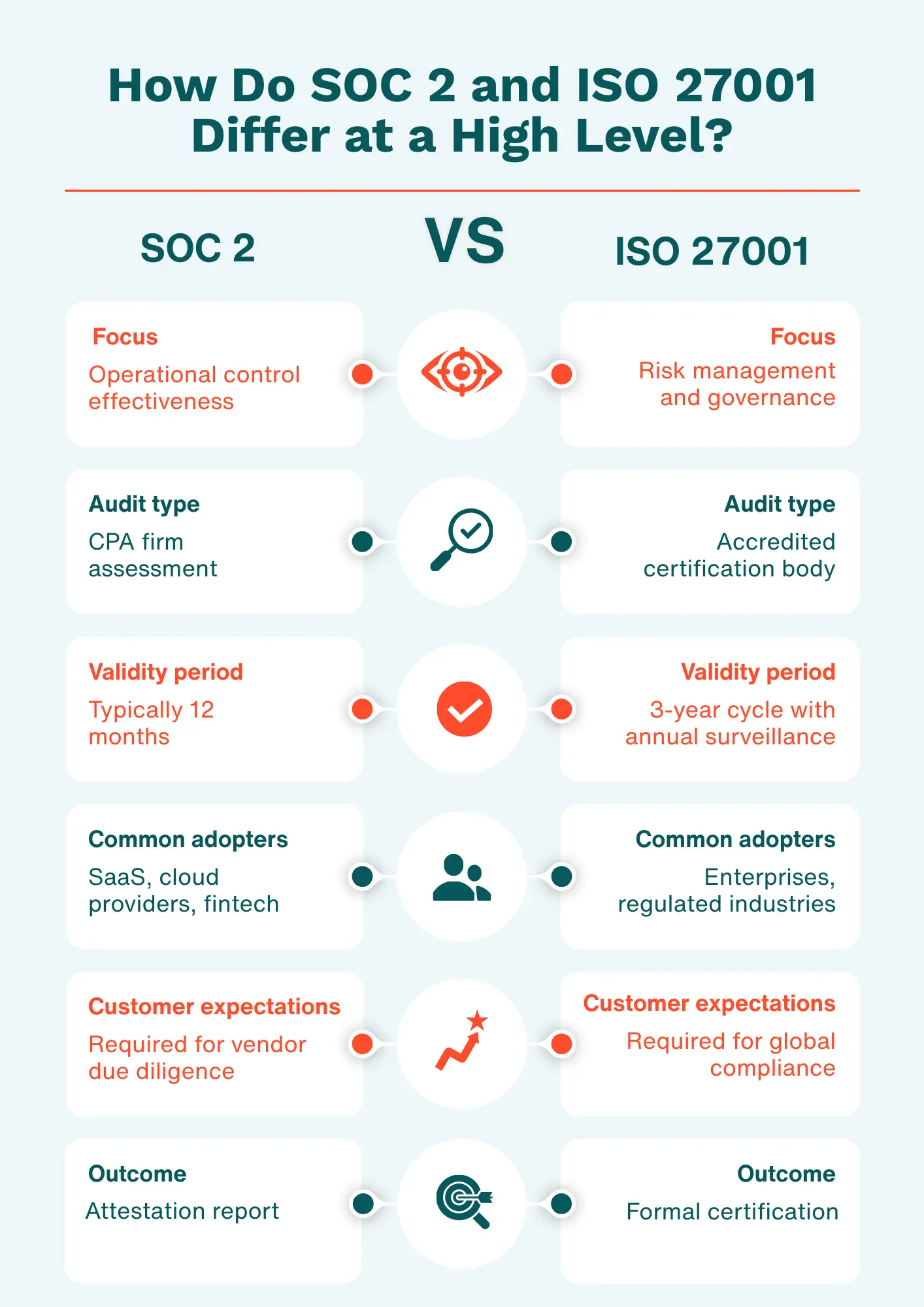
SOC 2 is typically better suited for SaaS and cloud-native organizations. Enterprise buyers often require SOC 2 reports during vendor risk assessments.
Multiple independent SaaS compliance reports show that a large majority of enterprise buyers, often 70–83% depending on survey and region, expect SOC 2 compliance before advancing vendor contracts.
This includes data showing 78%–83% of buyers prefer vendors with SOC 2 compliance. For deeper SaaS-specific considerations, see Application Security & Compliance: GDPR, SOC 2, and ISO.
ISO 27001 is better suited for organizations operating across multiple jurisdictions. It provides a common security language for regulators, partners, and customers worldwide.
ISO 27001 aligns closely with GDPR, NIS2, and regional data protection laws. Healthtech and fintech organizations often adopt ISO 27001 for international expansion.
Relevant guidance is available in ISO 27001 Certification Guide.
Yes, many organizations adopt both frameworks using shared controls. This approach reduces duplication and improves audit efficiency.
This hybrid approach is explained further in SOC 2 vs ISO 27001: A Practical Comparison.
Penetration testing validates whether security controls are effective in real-world scenarios.
Both SOC 2 and ISO 27001 increasingly expect regular testing.
According to IBM’s Cost of a Data Breach Report, organizations conducting routine penetration testing reduce breach costs by USD 1.2 million on average.
SOC 2 typically requires 3–6 months, while ISO 27001 often takes 6–12 months. Timelines vary based on organizational maturity and scope.
SOC 2 emphasizes control readiness and evidence collection. ISO 27001 requires policy development, risk assessments, and governance workflows.
ioSentrix provides continuous security validation across both frameworks. Its platform integrates penetration testing, evidence tracking, and risk insights.
The right framework depends on geography, customer expectations, and compliance maturity.
SOC 2 prioritizes operational trust, while ISO 27001 emphasizes structured risk management.
Many organizations adopt both to meet enterprise trust requirements and global compliance goals. A unified security validation strategy reduces cost, complexity, and audit friction.
Contact ioSENTRIX to align your security program with compliance expectations.