
Organizations working toward SOC 2 or ISO 27001 quickly realize something important:
Both frameworks expect strong evidence of penetration testing, but neither explains exactly what type of pentest you need.
This creates uncertainty for engineering teams, CISOs, and compliance managers trying to determine how deep their testing must go, which systems fall in scope, and how often they must repeat testing.
In this definitive guide, we break down what SOC 2 and ISO 27001 actually require, the types of penetration testing that satisfy auditors, and how ioSENTRIX supports organizations with in-depth security testing.
SOC 2 is an attestation standard developed by the AICPA.
It evaluates how effectively an organization protects customer data across the Trust Services Criteria, including Security, Availability, Confidentiality, Processing Integrity, and Privacy.
While the Security category is mandatory, organizations select additional categories based on customer expectations and service offerings.
SOC 2 reports—Type I or Type II—focus heavily on proof.
Organizations must demonstrate they have implemented effective security controls and that those controls operate consistently over time.
Penetration testing becomes a crucial piece of evidence because it validates the resilience of an organization's applications and infrastructure.
ISO 27001 is an internationally recognized certification for establishing and maintaining an Information Security Management System (ISMS).
It is far more prescriptive than SOC 2 and revolves around risk assessment, policy enforcement, and a continuous security improvement lifecycle.
The 2022 revision of ISO 27001 introduced updated Annex A controls emphasizing technical vulnerability management, secure configuration, and information security testing.
These updates make penetration testing not only expected but an essential element of proving ISMS effectiveness.
Where SOC 2 emphasizes operational proof, ISO 27001 emphasizes structured governance and risk treatment, both of which require technical validation through security testing.
This is one of the most common questions businesses ask during compliance preparation, and the answer is pretty clear.
SOC 2 does not explicitly mandate penetration testing within its textual criteria.
However, SOC 2 auditors consistently expect organizations to perform regular testing to satisfy multiple Trust Services Criteria related to risk assessment, monitoring, and vulnerability management.
In practice, SOC 2 reports almost always include evidence of:
This expectation aligns with ioSENTRIX's comprehensive pentesting methodology, which includes business logic analysis, exploit verification, remediation guidance, and vulnerability tracking.
All these deliverables are viewed as strong security assurance by the SOC 2 auditors.
Without penetration testing, SOC 2 auditors frequently flag gaps around the Security Trust Services Criteria, which can delay report issuance.
In contrast, ISO 27001 practically requires penetration testing as part of multiple Annex A controls, particularly those involving technical vulnerability management, system monitoring, and secure development practices.
Organizations must show they are regularly identifying, evaluating, and mitigating security weaknesses.
ISO 27001’s focus on real risk treatment means companies must show:
ioSENTRIX’s services include full stack assessments and application-layer security evaluations, which perfectly complement ISO 27001’s risk-based approach.
SOC 2 auditors look for testing that validates the company’s ability to protect customer data from unauthorized access, data corruption, or system abuse.
SOC 2-Relevant Pentests Include:
1. Web Application Penetration Testing
2. API Penetration Testing: Essential for SaaS, mobile apps, automation, and integrations.
3. External Network Pentesting: Validates internet-exposed assets, cloud environments, and production systems.
4. Internal Network Pentesting: Tests lateral movement, privilege escalation, and internal access risks.
5. Mobile Application Pentesting (When mobile apps are in scope): ioSENTRIX uses static, dynamic, and contextual testing to assess cryptography, server communication, and business logic flaws.
6. Infrastructure & Cloud Pentesting: Focuses on misconfigurations, excessive permissions, insecure architecture.
ISO 27001 requires security testing that supports the risk treatment plan. Because ISO 27001 assesses entire systems rather than just applications, pentesting must be broader.
ISO 27001-Relevant Pentests Include:
1. Full-Stack Security Testing: ioSENTRIX offers assessments covering application logic, OSS/libraries, infrastructure, web servers, and architecture layers (ideal for Annex A control validation).
2. Application Security Testing
3. Network / Infrastructure Pentesting: Validates network segmentation, identity controls, server security.
4. Mobile App & Thick-Client Pentesting
Mobile: Static + dynamic + API + logic testing
Thick client: Binary analysis, communication protocol testing, DLL hijacking risks
5. Cloud Environment Security Tests: Especially critical with ISO 27001’s updates emphasizing cloud access control and configuration security.
Choosing the right pentest requires aligning business systems with compliance scope.
Required when you have:
ioSENTRIX’s method maps application functionality, tests surface areas, correlates vulnerabilities, and evaluates business logic risk, all of which auditors value.
APIs pose one of the biggest risks for modern applications. Testing includes:
Mobile apps introduce unique threats:
ioSENTRIX’s hybrid testing approach checks both iOS and Android apps using dynamic, static, and contextual testing.
Includes:
ioSENTRIX performs both internal and external network assessments across cloud and hybrid environments.
If your organization uses desktop applications, heavy internal processors, or proprietary software, thick-client testing becomes essential.
ioSENTRIX evaluates:
Many companies ask:
Do we need a red team for SOC 2 or ISO 27001?
The answer is: Not required, but highly valuable if you want to evaluate your entire defensive posture.
ioSENTRIX’s red team engagements simulate real adversaries across:
This helps organizations measure SOC performance, incident response, and resilience.
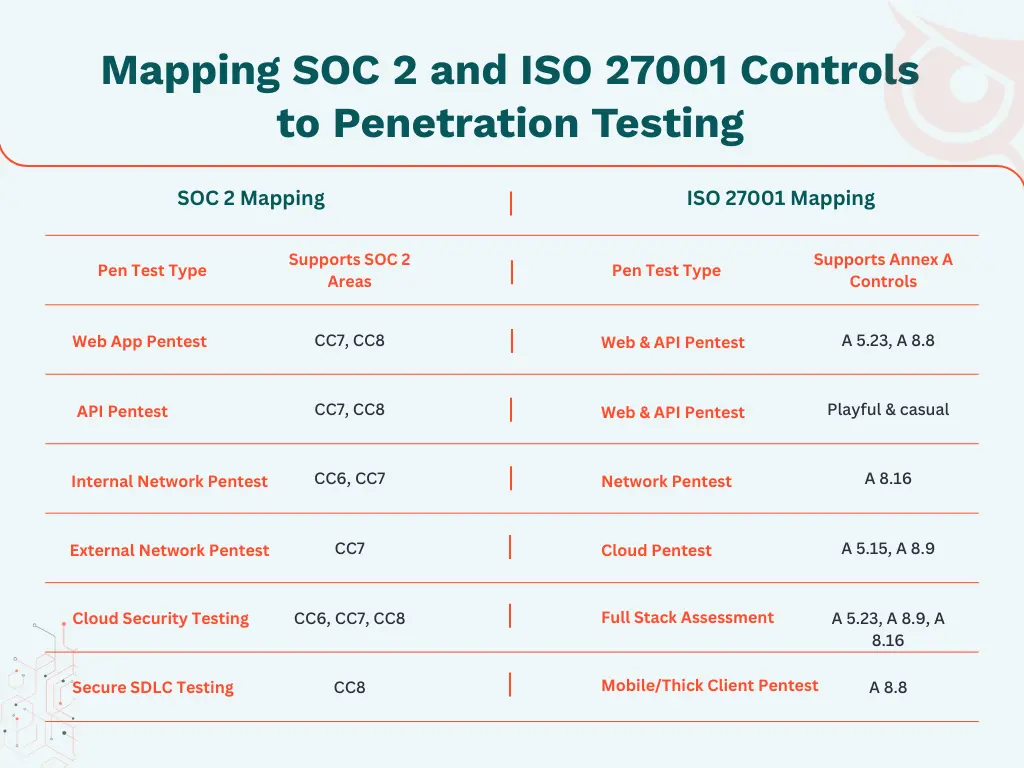
Compliance teams often struggle with mapping technical tests to audit controls. Below is a clear mapping to guide scoping decisions.
Web apps, APIs, mobile apps, thick clients, IoT, embedded systems, networks, cloud architectures. ioSENTRIX provides coverage across all modern technology stacks.
Our methodology prioritizes uncovering logic flaws that automated tools cannot detect, ensuring superior risk coverage and more meaningful findings.
ioSENTRIX provides:
These deliverables align perfectly with what SOC 2 and ISO 27001 auditors expect.
You may want to read: Why PTaaS Audit-Ready Deliverables is Essential for Compliance with Drata, Vanta, and Big 4 Standards?
ioSENTRIX also helps organizations implement Secure SDLC and DevSecOps practices, strengthening compliance with both SOC 2 and ISO 27001 by embedding security into development workflows.
ioSENTRIX has helped organizations around the world meet and exceed their SOC 2 and ISO 27001 requirements through deep technical penetration testing, architectural analysis, and secure development consulting.
If you're preparing for an audit, ioSENTRIX provides the expertise, reporting, and guidance needed to succeed.
Request a penetration test or contact with a security expert today.